Penetration Testing Services in the United States
What QAwerk testing team can do to help protect organizations from attacks?
Penetration Test Thoroughly
Relying solely on vulnerability scanning is not enough to guarantee the security of your system. Achieve complete protection with help from professional penetration testers. Let ethical hackers take part in your testing process before unknown intruders try to gain access without your knowledge.Think Like an Attacker
Pentesters are highly skilled professionals with the knowledge to pinpoint potential vulnerabilities in your software and IT infrastructure. Often, a simple security lapse or mistake by an employee is the door hackers use to enter and launch more damaging attacks.Secure Your Assets
QAwerk has the expertise to identify and prevent cyber threats, including those targeting critical business information. Their cybersecurity expertise can help you secure your most valuable assets in case of a threat.Why Penetration Testing in the USA
Secure Product Launch
A smooth product launch is essential for gaining the trust of consumers. To ensure this happens, businesses must take measures to secure their software against implicit cyber-attacks and protect sensitive data from being penetrated by third parties. Our testers in the USA conduct comprehensive security tests before a product's release to minimize possible problems down the road.
Secure Software Upgrades
Updating software is crucial to ensure its continued functionality. This process often involves releasing security patches. However, these updates can sometimes introduce new vulnerabilities that could potentially compromise sensitive data. Therefore, penetration testing must be conducted during every critical software release to identify and mitigate potential risks.
Reduced Downtime
Our quality penetration testing services in the USA will help you proactively prevent damage caused by service interruptions, which can lead to significant financial losses. DDoS attacks have become increasingly complex and sophisticated over time. As a result, businesses need to adopt a comprehensive approach to cybersecurity, with penetration testing as a crucial component.
Intact Company Image
Consumers are increasingly wary of sharing their sensitive data, and businesses that experience high-profile security incidents must invest significant resources to restore their reputation and regain customer trust. By engaging an ethical hacking firm, you can proactively identify and address vulnerabilities, preventing potential crises and safeguarding your business interests.
Improved Compliance
Businesses that operate digitally are required to comply with various cybersecurity regulations, such as SOC 2, PCI DSS, ISO/IEC 27001, and GDPR. All of these standards recognize the importance of validating a company's security posture through consistent penetration testing. Our specialists will help you understand which standards your business needs to meet and how best to satisfy them without incurring fines for non-compliance.
Greater Intelligence
Penetration testing is a valuable cybersecurity measure that can provide businesses with immediate insights into product vulnerabilities. This information allows them to allocate resources more effectively, providing early warning of potential security issues. By proactively identifying vulnerabilities, companies can adjust their priorities and strategies to minimize risk.
Case Studies from the United States
Looking for professional pentesters?
Contact UsTypes of Technologies We Provide
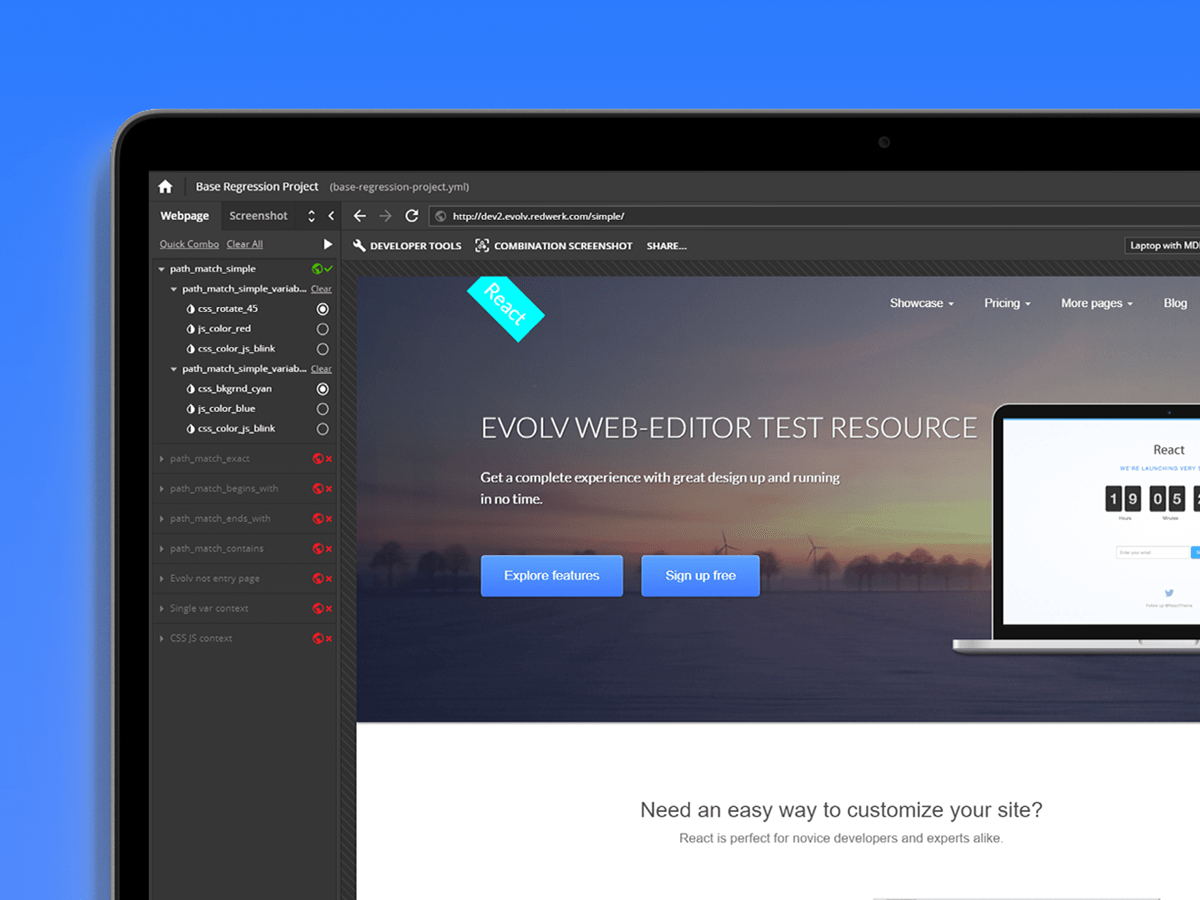
Black Box Testing
Grey Box Testing
White Box Testing
Tools and Technologies
Manual Testing
Automated Testing
Exploratory Testing
Integration Testing
Acceptance Testing
System Testing
Performance Testing
Regression Testing
Reliability Testing
Stress Testing
Load Testing
Unit Testing
Related in Blog
Looking for quality pentesting services in the USA?
Avert data breaches and future-proof your product against malicious attacks with QAwerk.
98%
VULNERABILITIES
DETECTED
1K+
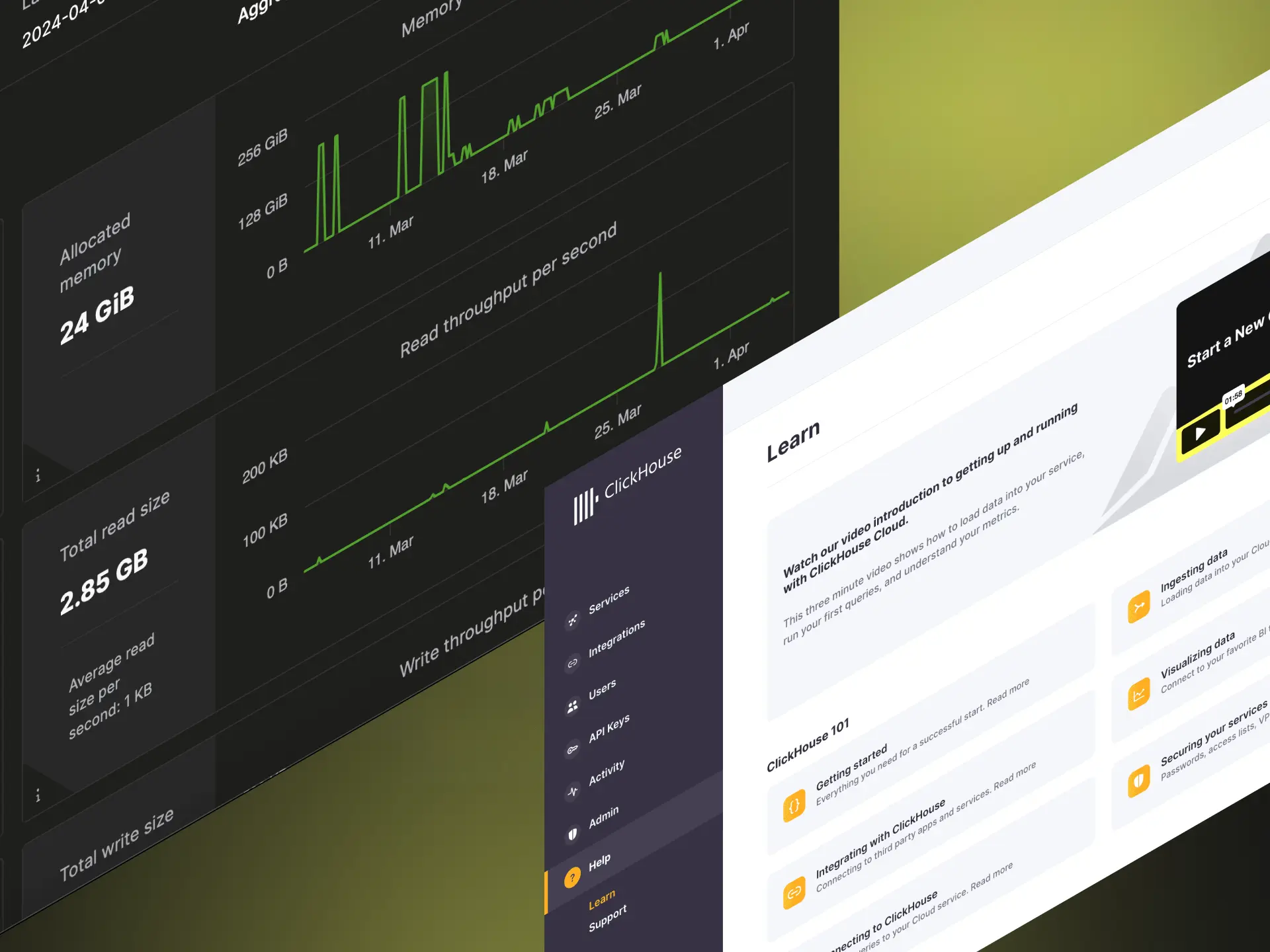
WEB APPS
TESTED
7
YEARS IN
CYBERSECURITY
30
PENTESTING TOOLS
MASTERED