What Makes Our Pentesting Unique
We don’t stop at surface-level scans. We approach your systems as real attackers would—combining manual exploitation with advanced tools and techniques. Our pentest as a service (PTaaS) simulates diverse threat scenarios to test the resilience of your infrastructure, code, and configurations.
Our Penetration Testing Services
Web Application Penetration Testing
Simulate internal and external attacks against your web application to assess its exposure to real-world threats. We test authentication flows, input validation, session management, and misconfigurations.
Static Application Security Testing (SAST)
We examine your source code without executing it, identifying insecure coding patterns, unvalidated inputs, and weak encryption before they reach production.
Network Penetration Testing
We imitate cybercriminal tactics to detect open ports, misconfigured firewalls, and exposure of critical data from outside your organization.
Cloud Security Penetration Testing
Expert penetration testing uncovers vulnerabilities in cloud infrastructure, configurations, IAM, and APIs—securing AWS, Azure, GCP, and more.
Mobile Application Penetration Testing
Our QA engineers reveal security flaws in iOS and Android apps, safeguarding user data and preventing unauthorized access with thorough pentesting.
API Penetration Testing
Thorough evaluation detects common vulnerabilities in APIs, like injection and broken authentication, keeping your backend safe from threats.
Pentesting Methods We Use
Black Box Testing
This testing method is perfect for simulating an attack by an external hacker who has no access to the source code and only a limited understanding of the network structure, software protection, and other security controls.
Grey Box Testing
Here, the attacker is aware of some internal processes and may have access to certain functionality. This scenario implies that the hacker is either a malicious employee or an external intruder who uses someone’s compromised credentials.
White Box Testing
This type of pentesting presupposes admin rights, access to server configuration files, software architecture, knowledge of data encryption mechanisms, etc. It is meant to discover those vulnerabilities hiding deep under the surface.








Security Code Reviews
Penetration Testing Types We Provide
External Pen Testing
Identify vulnerabilities in your public-facing infrastructure—such as websites, APIs, and cloud services—before attackers can exploit them. Our team simulates real-world threats to assess your exposure and provide concrete recommendations to strengthen your cyber defenses.
Internal Penetration Testing
Detect weaknesses that could be exploited from within your network, such as by disgruntled employees or compromised devices. We assess your company’s internal security posture, simulate lateral movement, and highlight gaps that may allow unauthorized access to sensitive data or critical systems.
Social Engineering Testing
Evaluate your team’s readiness against phishing, pretexting, and other manipulation tactics. We conduct ethical social engineering tests—including simulated phishing campaigns and physical attempts to access restricted areas—to measure awareness and improve your human firewall.
Penetration Testing for Compliance
Meet industry regulations with targeted penetration tests tailored for frameworks like PCI DSS, GDPR, HIPAA, and ISO 27001. We help you address specific audit requirements, remediate findings efficiently, and maintain compliance while reducing risk.
How We Work
In simple terms, here is how we perform a penetration test.
Selected Cases
Looking for a reliable penetration testing provider?
Contact UsWhy Choose Us as Your Penetration Testing Company
 Zero Disruption Promise
Zero Disruption Promise
Our penetration testing teams meticulously plan every assessment to prevent disruptions or downtime, ensuring your operations run smoothly while we safeguard your systems.
 Detailed Pentesting Reports
Detailed Pentesting Reports
We deliver clear, comprehensive penetration test reports that explain vulnerabilities in business terms and provide actionable remediation strategies tailored to your needs.
 Fast Turnaround on Results
Fast Turnaround on Results
Our penetration testing service guarantees swift delivery of your detailed report—faster than you can review all the documentation—meeting even the tightest deadlines.
 Security Experts, Not Just Testers
Security Experts, Not Just Testers
Our certified cyber security penetration testing professionals bring years of DevSecOps and real-world experience, going beyond basic testing for deeper, more reliable results.
 Compliance-Driven Testing
Compliance-Driven Testing
We customize pentesting services to align with your industry regulations and legal requirements, helping you achieve compliance and reduce risks effectively.
 Proven QA and Security Expertise
Proven QA and Security Expertise
Leveraging years of software QA discipline, we enhance penetration testing with rigorous methodologies, bridging innovation and security for modern AI-driven workflows.
Penetration Testing Tools We Use
External Penetration Testing Cost and Factors
Penetration testing pricing typically ranges between $10,000 to $70,000+, depending on factors such as:
Scope & Complexity
number of IP addresses, domains, systems
Depth of Testing
surface-level automated scans vs. deep manual exploitation
Testing Methodology
automated tools only vs. manual detailed tests
Expertise Level
certifications and experience of pentesters
Urgency
rush testing often costs extra
Retesting & Validation
included or additional cost
Other Services We Offer
Game Testing Services
Our QA engineers thoroughly test gameplay, mechanics, and user experience across platforms, ensuring bug-free, immersive gaming.
Compatibility Testing Services
We validate software performance across diverse devices, operating systems, and configurations to ensure seamless user experiences everywhere.
Regression Testing Services
We perform comprehensive regression tests to catch new issues after updates, keeping your software stable and reliable throughout its lifecycle.
Blockchain Testing Services
Our experts audit smart contracts, validate transactions, and verify security to ensure your blockchain applications are robust and fraud-resistant.
LLM Testing Services
We rigorously evaluate large language models for accuracy, bias, and safety to optimize AI reliability in high-stakes applications.
AI-Based Testing
Combining AI-powered tools with manual expertise, we accelerate bug detection, improve test coverage, and enhance overall software quality.
FAQ
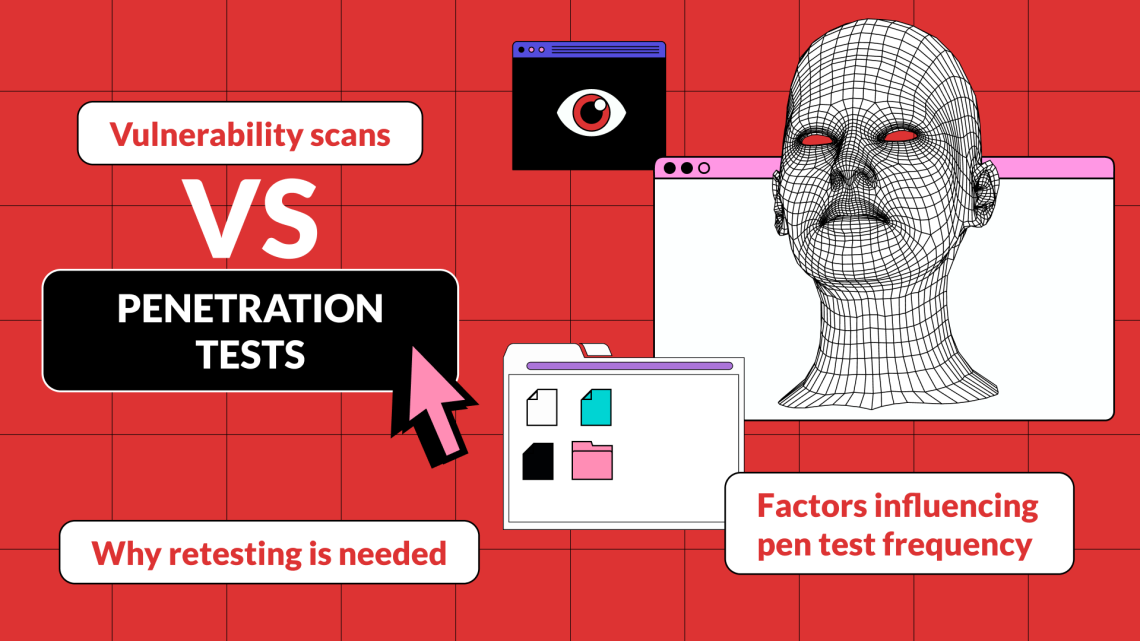
Why can’t I rely on automated vulnerability scanners alone?
Because they only check for known issues. Pentesting validates what’s truly exploitable.
Is penetration testing disruptive to our systems?
Not with QAwerk. We plan carefully, test in staging environments, and never interrupt production unless you request it.
How is pen testing different from vulnerability scanning?
Scanners list weaknesses. Pen tests show how those weaknesses can be exploited and what real damage they could cause.
Can we do our own penetration testing?
Only if your team includes experienced ethical hackers. Otherwise, external pen testing is more objective, efficient, and compliant.
How long does a penetration test take?
Depending on the scope, 5 to 15 business days for most apps.
What steps should a business take after receiving a penetration testing report?
Upon receiving a penetration test report, businesses should prioritize and remediate critical vulnerabilities immediately, patching systems and updating security measures. It’s crucial to then verify these remediations through re-testing and update internal security policies and procedures based on the findings. Finally, document everything and schedule regular penetration tests to ensure continuous security improvement.
Related in Our Blog
Worried about hidden cyber risks?
Let QAwerk uncover vulnerabilities before attackers do. Get your systems secure with expert penetration testing.
98%
VULNERABILITIESDETECTED
1K+
WEB APPSTESTED
30
PENTESTING TOOLSMASTERED
10+
YEARS INCYBERSECURITY