Expert Penetration Testing Services for Software Security in London
What can we do to help protect organizations from attacks?
Test Thoroughly
Relying solely on vulnerability scanning is not an effective cybersecurity strategy. While it's an important first step, achieving complete security requires the help of professional penetration testers. Let ethical hackers take part in your testing process before unknown intruders show up unannounced.Think Like Hacker
Pentesters are highly skilled professionals who will scrutinize your software and IT infrastructure in order to identify potential vulnerabilities. Often, a simple security lapse or mistake by an employee is the doorway hackers use to gain access to the system and launch more expensive attacks.Secure Assets
QAwerk possesses the skill set necessary to identify and prevent cyber threats - including those that target critical business information. Their expertise in cybersecurity provides guidance on how to secure your most valuable assets, should a threat arise.Why Penetration Testing in London
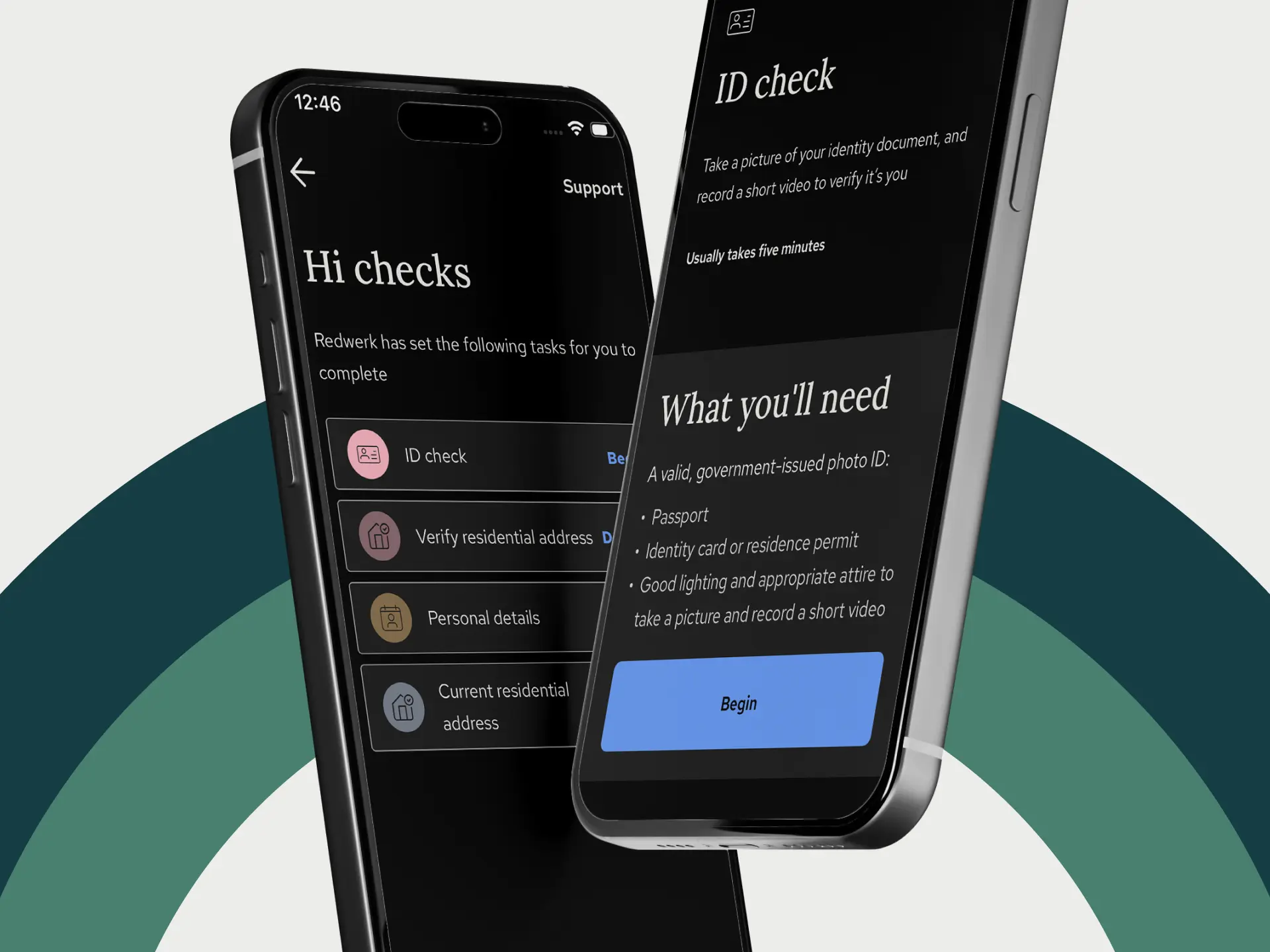
Secure Product Launch
A smooth product launch is essential for gaining the trust of consumers. To ensure this happens, businesses must take measures to secure their software against potential cyber-attacks and protect user data from being accessed by third parties. Our pentesters in London conduct comprehensive security tests prior to a product's release in order to minimize possible problems down the road.
Secure Software Upgrade
Updating software is important for ensuring that it remains functional, and this process often includes issuing security patches. These updates may introduce new vulnerabilities into the system, which could potentially jeopardize sensitive user data. Therefore, penetration testing must be carried out during every mission-critical release of software in order to safeguard against potential threats.
Reduced Downtime
Our quality penetration testing services in London will allow you to proactively prevent any damage caused by service interruption – this alone results in losses totaling 400,000 dollars per hour. DDoS attacks have become more complex and scalable over the years; as such, businesses now need to take a multifaceted approach to cybersecurity with pentesting being at the top of that list.
Intact Company Image
Security breaches can cause both financial and reputational losses for companies. Consumers do not want their sensitive data shared on the dark web, so those companies that suffer from headline-making security incidents must allocate extra resources to restoring their good name and regaining customer trust. By hiring an ethical hacking company, you can avert a crisis and protect your business interests in this way.
Improved Compliance
Businesses that operate digitally are required to comply with various cybersecurity regulations, such as SOC 2, PCI DSS, ISO/IEC 27001, and GDPR. All of these standards recognize the importance of validating a company's security posture through consistent penetration testing. Our specialists will help you understand which standards your business needs to meet and how best to satisfy them without incurring fines for non-compliance
Greater Intelligence
Pentesting is a beneficial cybersecurity measure that can provide businesses with an instant snapshot of product vulnerabilities. This information allows them to allocate resources more effectively, allowing them forewarning of potential security issues. By being aware of product weaknesses beforehand, companies can shift their focus and priorities as needed in order to minimize risk.
Case Studies from London
Looking for professional pentesters?
Contact UsTools
Jira
Figma
Charles
Android Studio
Bitrise
TestFlight
Related in Blog
Looking for quality pentesting services in London?
Avert data breaches and future-proof your product against malicious attacks with QAwerk.
98%
VULNERABILITIES
DETECTED
1K+
WEB APPS
TESTED
7
YEARS IN
CYBERSECURITY
30
PENTESTING TOOLS
MASTERED