- June 4, 2026
- 12 min read
If you are wondering why LLM red teaming tools are something you must know about today, consider this: cybercrime costs are forecast to exceed $10.5 trillion in 2025, with LLM vulnerabilities now part of that trajectory.
- June 2, 2026
- 16 min read
One sentence. That’s all it took to convince a car dealership’s AI assistant to “agree” to sell a $76,000 SUV for a single dollar back in December 2023.
- May 19, 2026
- 10 min read
Not sure whether to run a penetration testing vs vulnerability scanning? Check out this breakdown of what each covers and when to use which.
- March 12, 2026
- 10 min read
Your mobile app is live. People are downloading it, using it daily, maybe even paying through it. But here's the uncomfortable question: how safe is it, really? This is where mobile application security testing tools come in, as they can help ensure you are 100% confident in your product.
- February 4, 2026
- 11 min read
Founders run penetration tests because surprises in production cost real money. A good penetration test lets you see your product the way an attacker would, without the chaos of an actual breach. It pressures your system with the same discipline used in serious QA: controlled conditions, clear evidence, and no room for wishful thinking.
- January 22, 2026
- 8 min read
Today, we’ll talk about penetration testing myths and how believing in them might compromise your system’s defenses and, ultimately, lead to your business’s ruin. The dangers of cyberattacks are real, and you must have the best defenses you can afford.
- January 19, 2026
- 10 min read
Penetration testing with LLM is becoming more popular, just like everything else powered by AI. The processing capabilities offered by this technology are unprecedented, and its potential only grows as it attracts billions of dollars in investment every year.
- January 12, 2026
- 10 min read
If you follow the news in the technology world, you wouldn’t question why open source security tools are growing in number, because you’ve seen a huge number of stories about data breaches or websites being hacked. That’s because, no matter how far technology has come, hacking is not lagging behind. In fact, in 2025, the average cost of a data breach reached over $4.4 million. Therefore, if you want your software to be safe, you need to be one step ahead.
- January 7, 2026
- 14 min read
Web applications have become the backbone of modern business operations. Consequently, they are a primary target for cybercriminals. According to the latest report from Verizon, application attacks and credential theft are the root causes of 12% of confirmed data breaches globally, with phishing and AI-powered social engineering further escalating the threat landscape.
- July 19, 2024
- 6 min read
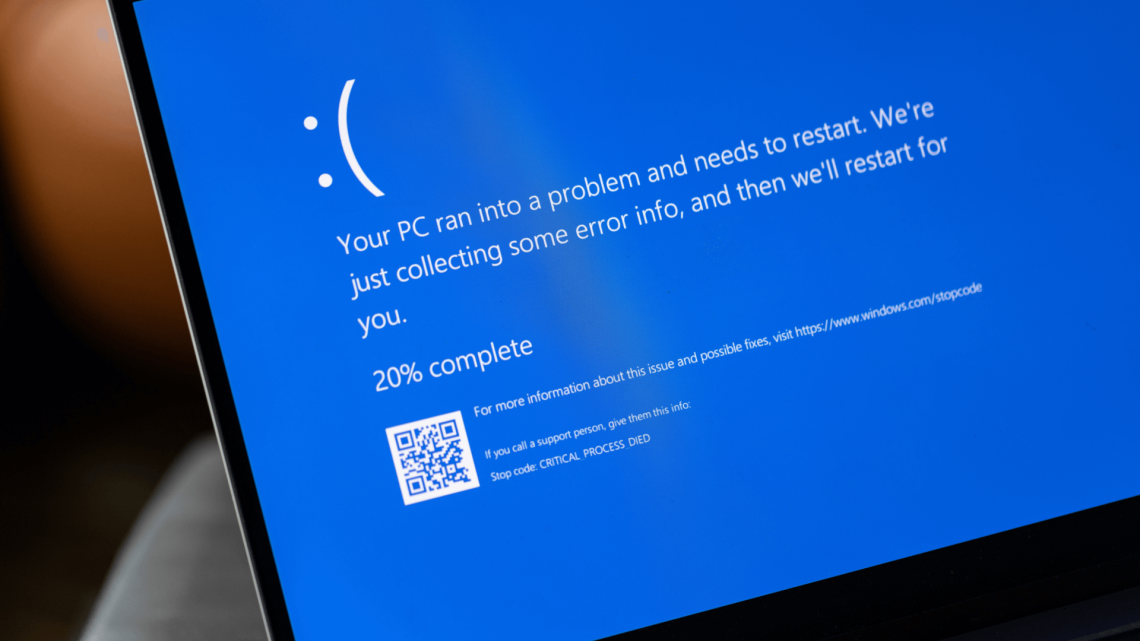
Just yesterday, the idea that a single IT misstep could cripple companies across entire industries might have seemed like a huge overstatement. However, the recent Microsoft outage is a stark reminder of how interconnected our world is. On July 19th, 2024, a faulty security update from CrowdStrike wreaked havoc on Microsoft Windows systems worldwide. How could such an IT catastrophe unfold? Let’s dive in and explore the causes.